OPNsense IP Addresses from ASN
This script creates a text file of all IPs associated with any number of ASNs for use in creating selective routing rules within OPNsense. Use it if you want to route, say, every Facebook IP address regardless of domain name to a specific firewall rule.
Why use selective routing rules?
Some scenarios in which you may want to use this script are:
- Routing outbound traffic to specific company's ASN through a VPN
- Allowing incoming traffic from a specific company's ASN
Limitations
This script is a hammer, not a scalpel. It will add ALL IP ranges from the targeted companies to the rule. To create rules for specific FQDNs, add them to a Host(s) alias in OPNsense --> Firewalls --> Aliases You can read this document to learn more about ASNs.
How it works
Gathers the IP ranges associated with the ASNs specified in the configuration file and writes these IP addresses into a text file that can be read from an OPNsense URL Table (IPs) alias.
Installation and Usage
These instructions are for installing directly on a device running OPNsense.
- SSH in to OPNsense
- Install Git:
pkg install git - Clone this repository:
git clone https://github.com/natelandau/opnsense-IPs-from-ASN.git
- Enter the directory:
cd opnsense-IPs-from-ASN - Edit the configuration file (
SETTINGS.conf) to reflect your preferences - Create a symbolic link to
/usr/local/bin/sudo ln -s \ ${HOME}/opnsense-IPs-from-ASN/ips_from_asn.sh \ /usr/local/bin/ips_from_asn.sh - Enable use in OPNsense cron
sudo ln -s \ ${HOME}/opnsense-IPs-from-ASN/actions.d/ips_from_asn.conf \ /usr/local/opnsense/service/conf/actions.d/actions_ips_from_asn.conf - Restart config.d:
sudo service configd restart - Run the script using configd. If it works, you should see a file created at the location you specified in the settings.
sudo configctl ips_from_asn run
Default Configuration
The default configuration assumes you are running this script directly within OPNsense
A file named ips_from_asn.txt is created containing all the IP addresses. This file is written to a directory named custom_aliases will is created at OPNsense's web root (/usr/local/www). This can be customized with the OUTPUT_FILE variable
Other settings should be self-evident within SETTINGS.conf
Default ASNs
| Company | ASN |
|---|---|
| AppNexus | AS29990 |
| Bytedance (TikTok) | AS396986 |
| AS32934 | |
| Facebook Corp | AS54115 |
| Facebook-offnet | AS63293 |
| AS15169 | |
| Oracle | AS792 |
| AS35995 |
To add a new company's ASN, follow these steps.
- Copy an IP address from the company
- Paste it into this tool: https://hackertarget.com/as-ip-lookup/
- Add the ASN number to the
ASN_LISTarray inSETTINGS.conf
NOTE: Many companies do not have their own ASN. If the ASN for your sample IP is a CDN (Akamai, Fastly,Cloudflare, etc), or a cloud hosting provider you will be routing ALL services hosted within that ASN.
CLI Flags
-h, --help Display help and exit
-n, --dryrun Non-destructive. Makes no permanent changes.
-q, --quiet Quiet (no output)
-v, --verbose Output more information. (Items echoed to 'verbose')
Configuring OPNsense
To use this file in an OPNsense firewall rule, follow these steps
- Log in to your OPNsense web administration area
- Navigate to
Firewall --> Aliases - Click the
+button to add a new alias - Name it something
- Select type
URL Table (IPs) - Set it to
30 daysas aRefresh Frequency(These IPs don't update frequently) - In the
Contentfield add:https://127.0.0.1/custom_aliases/ips_from_asn.txt - Add a
Descriptionif you want SaveandApplythe alias- Build whatever firewall rules you want
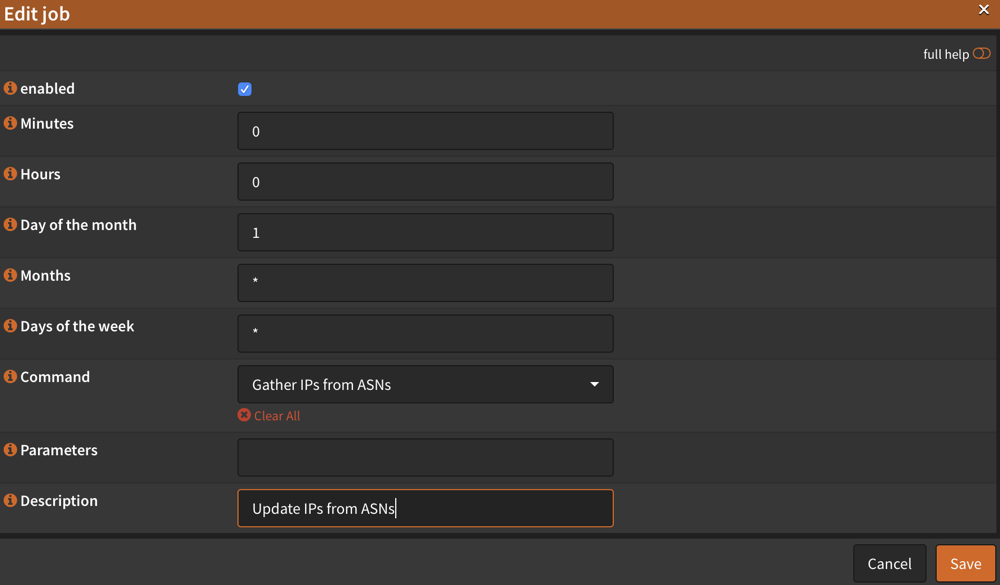
Add the script to cron
To update these IPs, you need to add the script to cron
- Log in to your OPNsense web administration area
- Navigate to
System --> Administration --> Cron - Click the
+button to add a new cron task - Change
Day of the Monthto1and leave everything else as a default