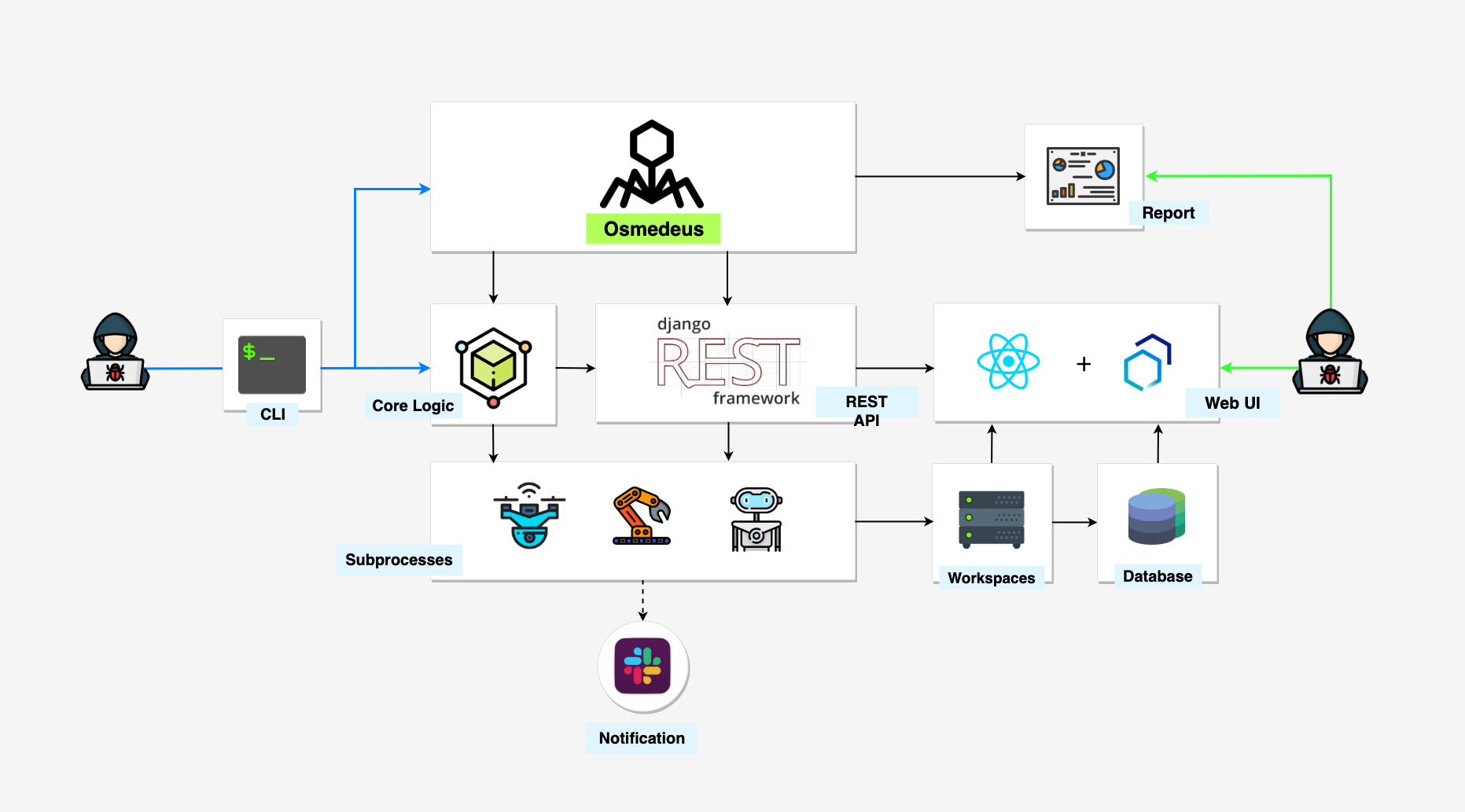
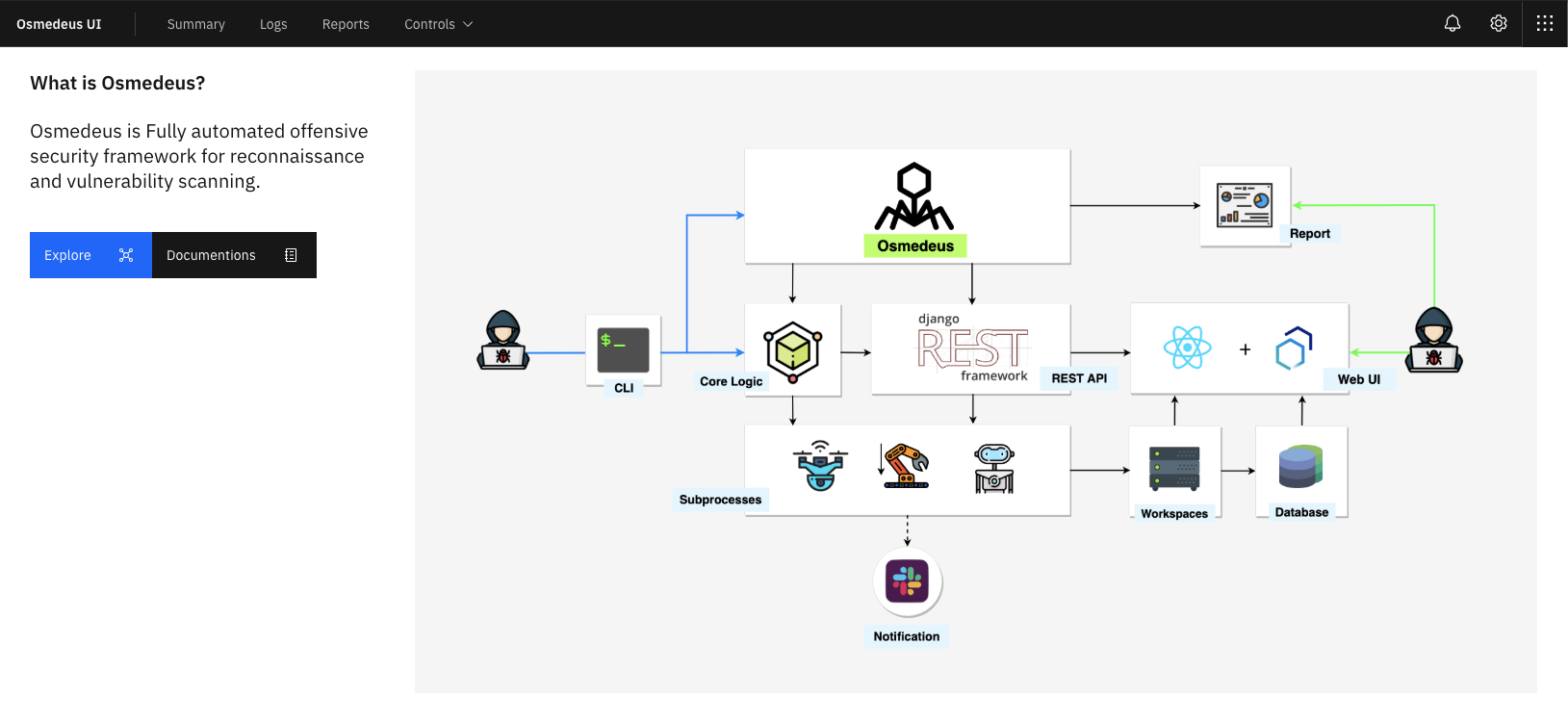
Osmedeus allows you automated run the collection of awesome tools to reconnaissance and vulnerability scanning against the target.
This version will soon be deprecated. Please check out the Next Generation of it at @OsmedeusEngine
git clone https://github.com/j3ssie/Osmedeus
cd Osmedeus
./install.sh
This install only focus on Kali linux, check more install on Usage page.
NOTE: You might need to do sudo su before install or using this otherwise you might get issues with dependency problems.
Check out docker-osmedeus by mabnavarrete
If you have no idea what are you doing just type the command below or check out the Advanced Usage
./osmedeus.py -t example.com
- Subdomain Scan.
- Subdomain TakeOver Scan.
- Screenshot the target.
- Basic recon like Whois, Dig info.
- Web Technology detection.
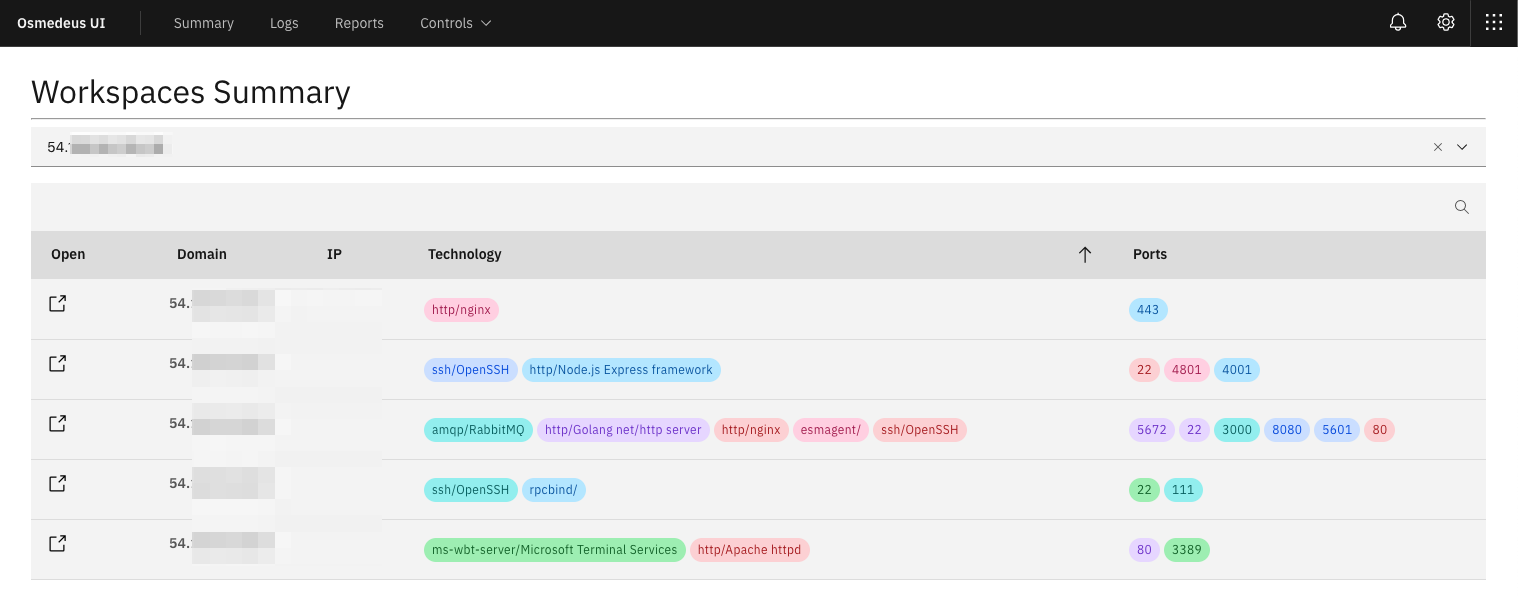
- IP Discovery.
- CORS Scan.
- SSL Scan.
- Wayback Machine Discovery.
- URL Discovery.
- Headers Scan.
- Port Scan.
- Vulnerable Scan.
- Seperate workspaces to store all scan output and details logging.
- REST API.
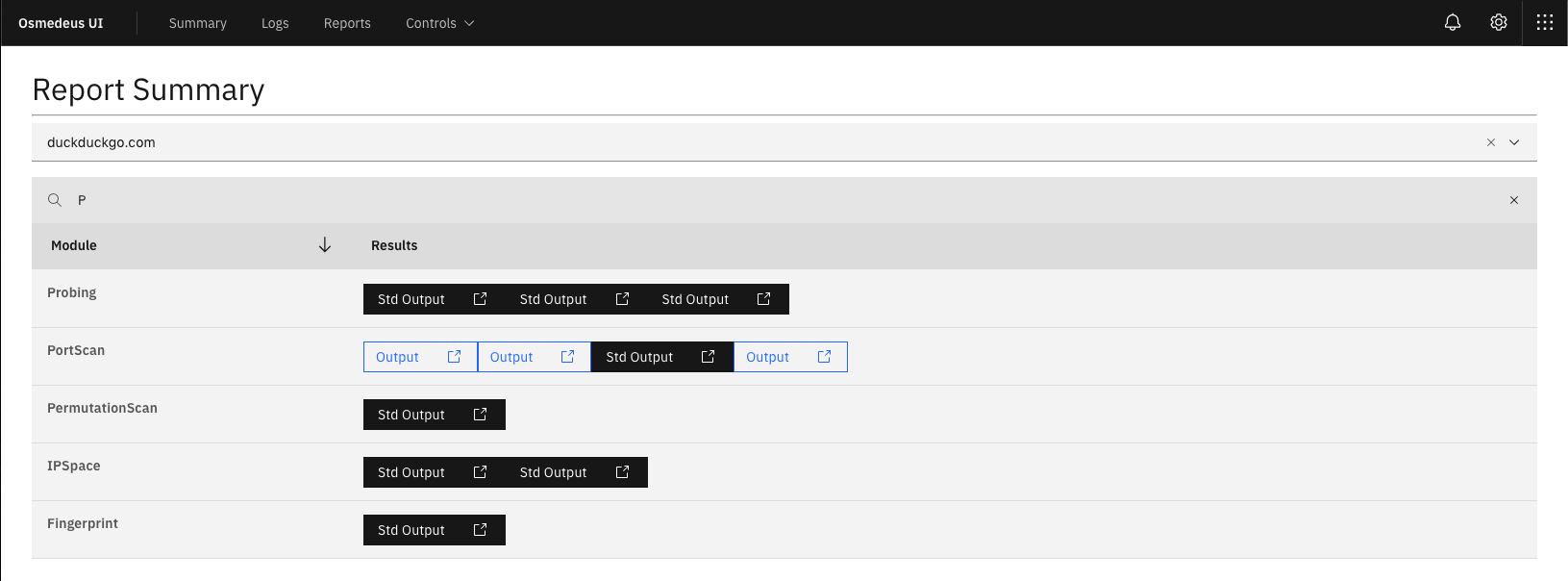
- React Web UI.
- Support Continuous Scan.
- Slack notifications.
- Easily view report from commnad line.
Check this Documentation for more detail about each module.
If you love my tool and would like to support my work. Become a backer and you will appear here.
# normal routine
./osmedeus.py -t example.com
./osmedeus.py -T list_of_target.txt
# normal routine but slow speed on all moddule
./osmedeus.py -t example.com --slow 'all'
# normal routine but exclude some modules
./osmedeus.py -t example.com -x 'linkfinding,dirb'
# direct mode examples
./osmedeus.py -m subdomain -t example.com
./osmedeus.py -m portscan -i "1.2.3.4/24"
./osmedeus.py -m "portscan,vulnscan" -i "1.2.3.4/24" -w result_folder
# direct list mode examples
./osmedeus.py -m portscan -I list_of_targets.txt
./osmedeus.py -m portscan,vulnscan -I list_of_targets.txt
./osmedeus.py -m screen -I list_of_targets.txt -w result_folder
# report mode
./osmedeus.py -t example.com --report list
./osmedeus.py -t example.com --report export
./osmedeus.py -t example.com --report sum
./osmedeus.py -t example.com --report short
./osmedeus.py -t example.com --report full
What to do next after do recon? Check out my scanner Jaeles.
Most of this tool done by the authors of the tool that list in CREDITS.md. I'm just put all the pieces together, plus some extra magic.
This tool is for educational purposes only. You are responsible for your own actions. If you mess something up or break any laws while using this software, it's your fault, and your fault only.
Please take a look at CREDITS.md
Please take a look at CHANGELOG.md
If you have some new idea about this project, issue, feedback or found some valuable tool feel free to open an issue for just DM me via @j3ssiejjj.
This project exists thanks to all the people who contribute. [Contribute].
Become a financial contributor and help us sustain our community. [Contribute]
Support this project with your organization. Your logo will show up here with a link to your website. [Contribute]