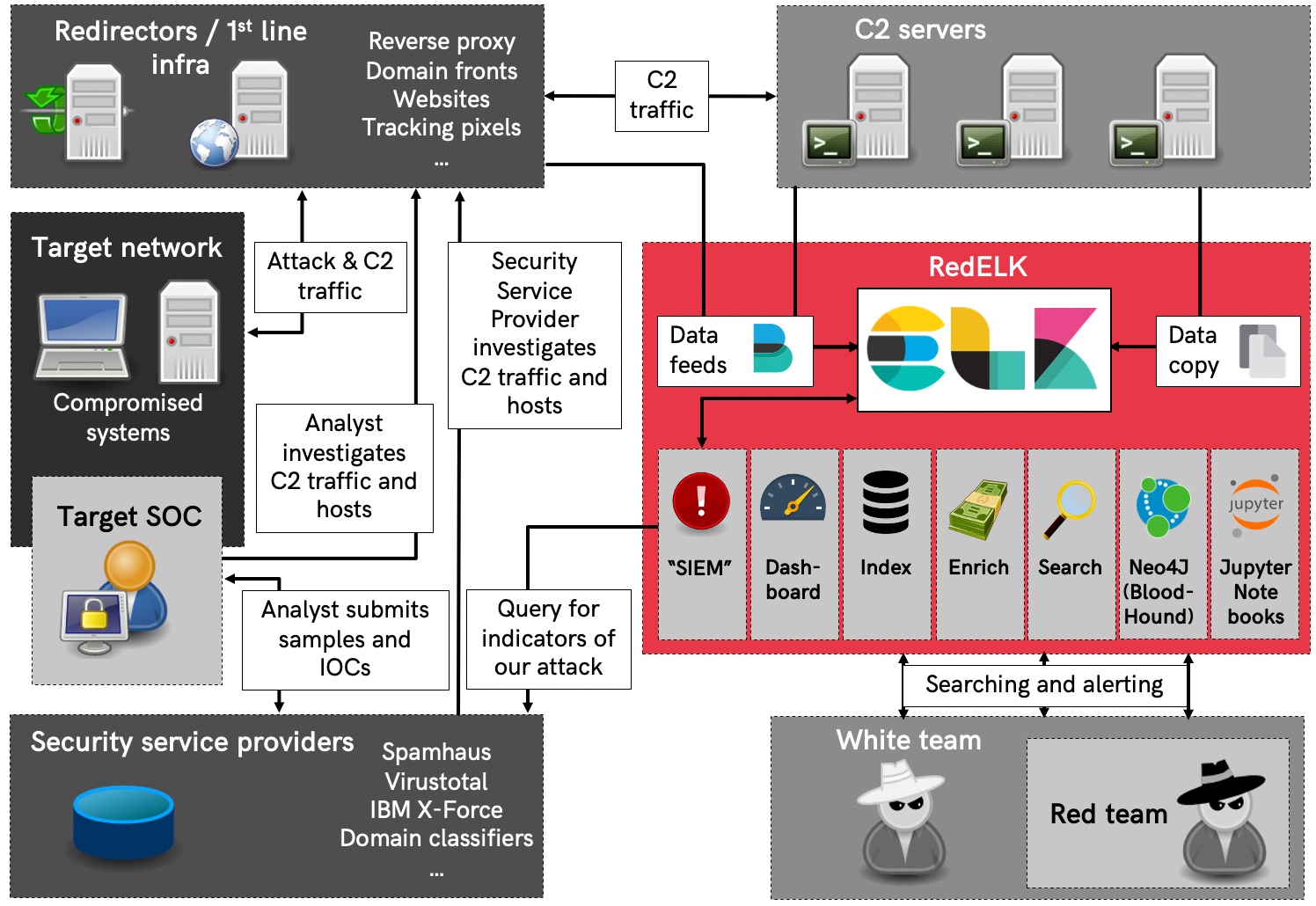
Red Team's SIEM - tool for Red Teams for tracking and alarming about Blue Team activities as well as enhanced usability in long term operations.
- Enhanced usability and overview for the red team operators by creating a central location where all relevant operational logs from multiple teamservers are collected and enriched. This is great for historic searching within the operation as well as giving a read-only view on the operation (e.g. for the White Team). Especially useful for multi-scenario, multi-teamserver, multi-member and multi-month operations. Also, super easy ways for viewing all screenshots, IOCs, keystrokes output, etc. \o/
- Spot the Blue Team by having a central location where all traffic logs from redirectors are collected and enriched. Using specific queries its now possible to detect that the Blue Team is investigating your infrastructure.
Check the wiki for info on usage or one the blog posts or presentations listed below:
- Blog part 1: Why we need RedELK
- Blog part 2: Getting you up and running
- Blog part 3: Achieving operational oversight
- SANS Hackfest 2020: Super charge your Red Team with RedELK video and slides
- Hack in Paris 2019: Who watches the Watchmen video and slides
- x33fcon 2019 Catching Blue Team OPSEC failures video and slides
- BruCon 2018: Using Blue Team techniques in Red Team ops video and slides
Check the wiki for manual installation manual. There are also Ansible playbooks maintained by others:
- RedELK Server playbook - maintained by one of RedELK's developers
- RedELK Client playbook - maintained by one of RedELK's developers
- ansible-redelk - maintained by curi0usJack/TrustedSec
Here's a conceptual overview of how RedELK works.
This project is developed and maintained by:
- Marc Smeets (@MarcOverIP on Github and Twitter)
- Mark Bergman (@xychix on Github and Twitter)
- Lorenzo Bernardi (@fastlorenzo on Github and Twitter)
We welcome contributions! Contributions can be both in code, as well as in ideas you might have for further development, alarms, usability improvements, etc.