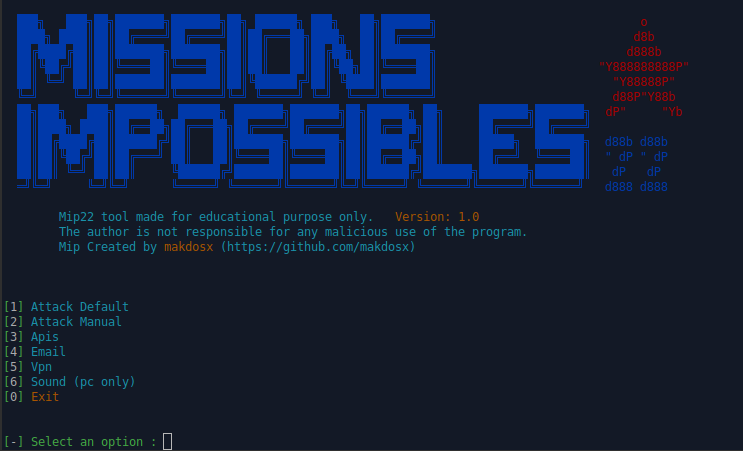
69 default websites, clone any site with manual method, mask link with subdomains, url shortener, audio notice for view the credentials live, music in background etc...
The program is made for educational purposes only for to see how the phishing method works. Any unnecessary use of the program is prohibited and the manufacturer has no responsibility for any illegal use by anyone. Use the tool at your own risk and avoid any sloppy actions.
Installation on Gnu / Linux OS.
On terminal
sudo su git clone https://github.com/makdosx/mip22.gitchmod -R 777 mip22 cd mip22bash mip22.sh
Installation on Android OS.
On Termux
git clone https://github.com/makdosx/mip22.gitchmod -R 777 mip22 cd mip22 bash mip22.sh
Mip22 is a modern and advanced cyber security program for computers with Gnu / Linux operating system and mobile phones and tablets with android operating system, for educational purposes.
Details
- Automatic method
- Manual Method
- Tunnels Setup
- Email Services
- Vpn instructions
- Sound Efects (only for pc)
- Automatic method
Easy to use via terminal.
Automatic cloned services.
It has 69 ready cloned electronic services, including social networks, e-mails, cloud, multumedia etc etc.
- Manual Method
Cloning services manually by cloning the service you want. Easy to use through browser service.
-
Tunnels Setup
It has 3 tunnels to promote these services from the local server to the internet.
It has ready api for the installation of some tunnels.
It has url shortener for hide the links -
Email Services
It has 3 well-known external email services found on the internet where you can visit to send an email. -
Vpn instructions
It has various instructions fron vpn on Android OS. -
Sound Efects (only for pc)
It has various effects such as music in the background. -
Notifications

For instant data access during an attack, when someone logs in, an alarm sounds so users do not have to look at the terminal all the time to see the data. (At this time Computer compatible only)