Amazon Elastic Container Registry Private Registry Authentication provides a temporary authorization token valid only for 12 hours. This operator refreshes automatically the Amazon ECR authorization token before it expires, reducing the overhead in managing the authentication flow during the container image build process.
This operator uses Amazon ECR GetAuthorizationToken API to create or update the secret, linked to an OpenShift service account that can transparently perform container image builds.
- Create an Amazon ECR private repository
- Create An OpenShift Cluster
- Configure AWS authentication method. Two options:
- Install the Operator SDK CLI
oc new-project ecr-secret-operator
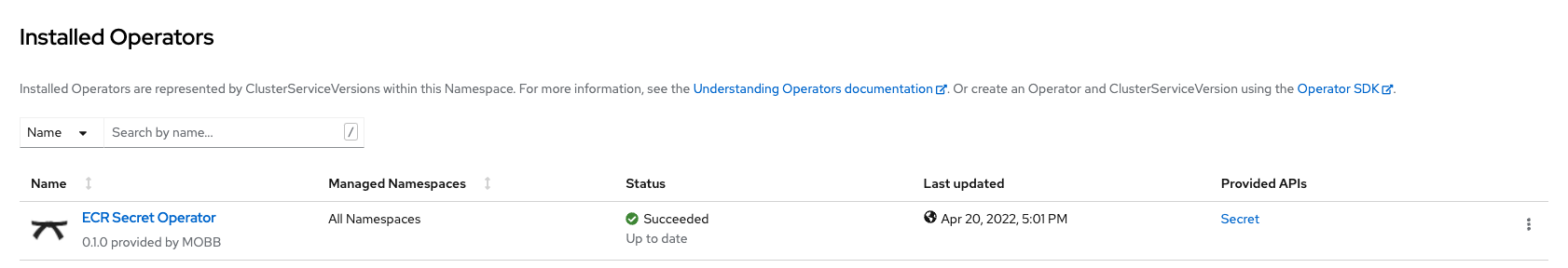
operator-sdk run bundle quay.io/mobb/ecr-secret-operator-bundle:v0.3.2apiVersion: ecr.mobb.redhat.com/v1alpha1
kind: Secret
metadata:
name: ecr-secret
namespace: test-ecr-secret-operator
spec:
generated_secret_name: ecr-docker-secret
ecr_registry: [ACCOUNT_ID].dkr.ecr.us-east-2.amazonaws.com
frequency: 10h
region: us-east-2oc create -f samples/ecr_v1alpha1_secret.yamlA Docker registry secret is created by the operator temporarily and the token is patched every 10 hours
oc get secret ecr-docker-secret
NAME TYPE DATA AGE
ecr-docker-secret kubernetes.io/dockerconfigjson 1 16hLink the secret to builder
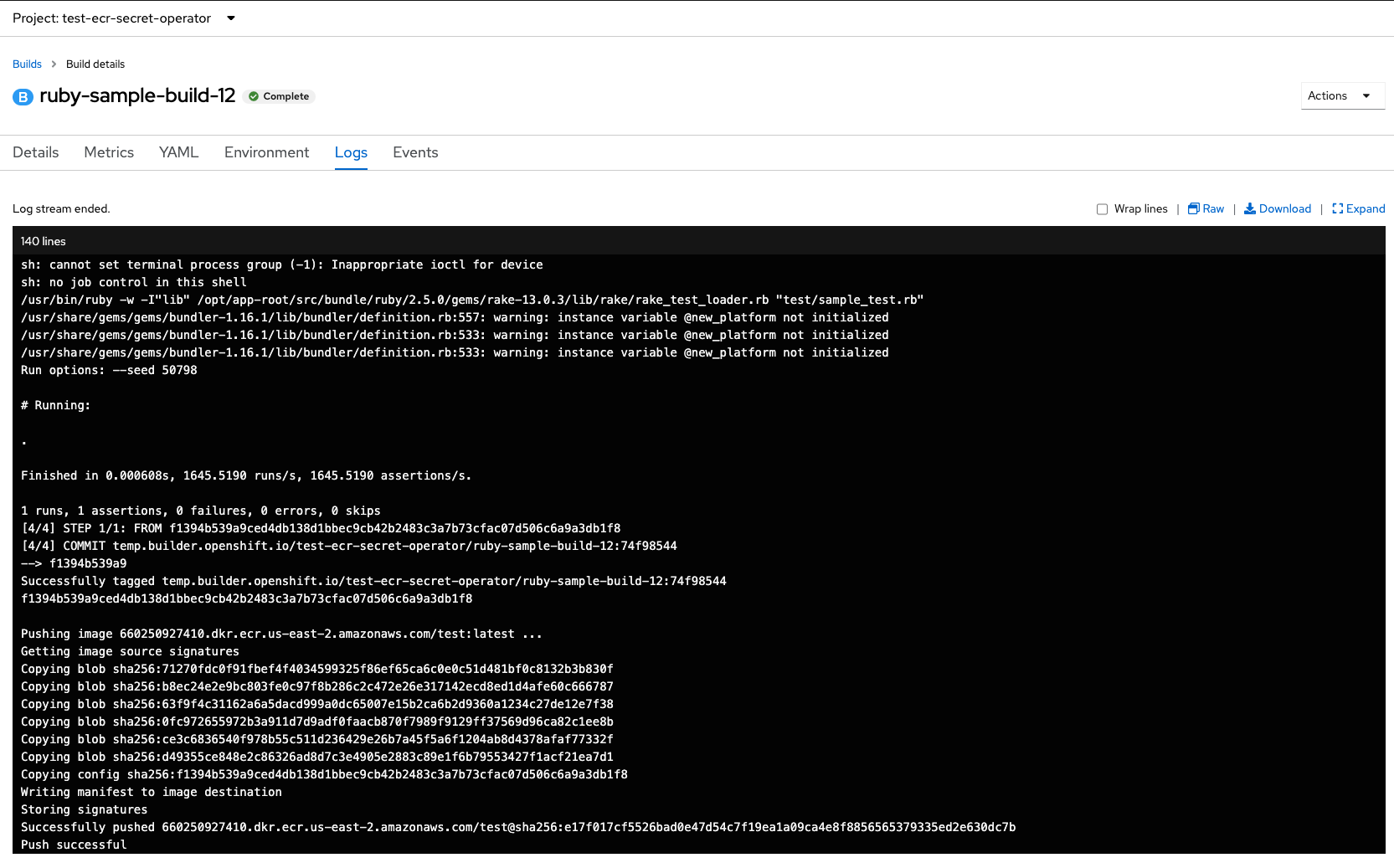
oc secrets link builder ecr-docker-secret Configure build config to point to your Amazon ECR Container repository
oc create imagestream ruby
oc tag openshift/ruby:2.5-ubi8 ruby:2.5
oc create -f samples/build-config.yaml
oc start-build ruby-sample-build --waitThe build should succeed and push the image to the the private Amazon ECR Container repository