Use Defender for Cloud Apps & create a file policy for detection of sharing US PII. Set email alert.
Project consists of a creating a Risk-based access policies as a part of Azure AD Identity Protection policies. Risk-based access policies, there are two types of risk policies in Azure Active Directory (Azure AD) Conditional Access we can set up to automate the response to risks and allow users to self-remediate when risk is detected: Sign-in risk policy and User-risk policy. In this practical, it is auto applying for High risk level.- Microsoft 365 Defender portal
- File policy for cloud apps can be created or modified by anyone assigned the following roles:
- Security Administrator
- Global Administrator
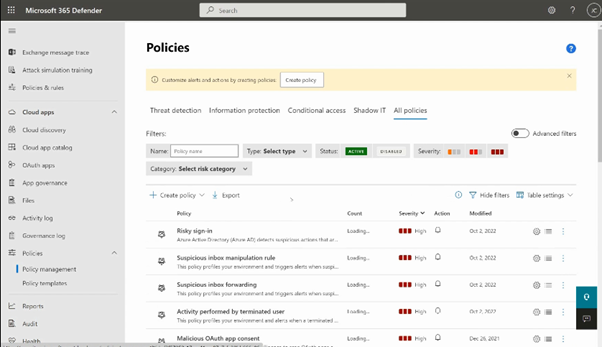
- Go to Microsoft 365 defender
- Cloud apps section --> select policies --> policies management
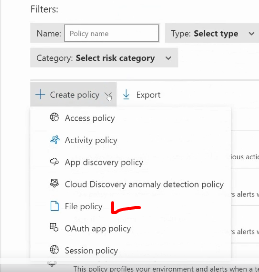
- Create policy --> select category ‘file policy’
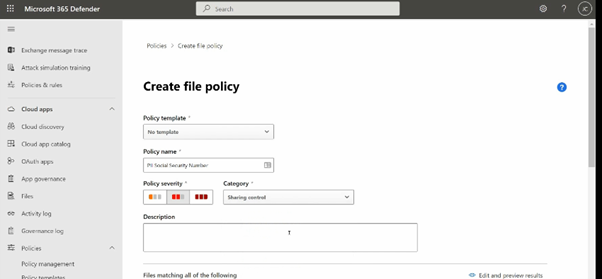
- Give a name, select a ‘sharing control’ as category
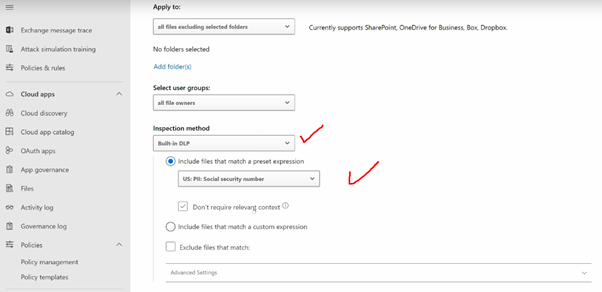
- Select users-groups, select inspection method & US : PII Social security number
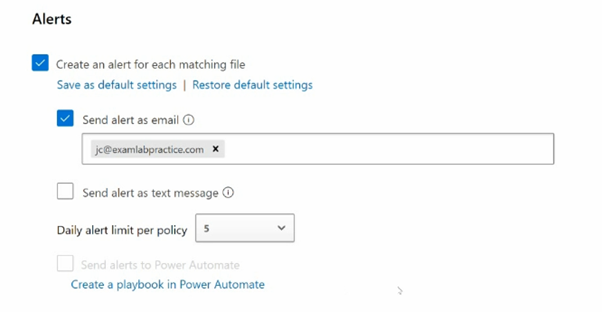
- Select alert as email and add email id of recipient
- Create
Policy Management:
Create a new Policy:
Give a name:
Select Users and Inspection method:
Alert settings: