A Collection of Vulnerabilities in ERC20 Smart Contracts With Tokens Affected
Read the docs in Chinese: https://github.com/sec-bit/awesome-buggy-erc20-tokens/blob/master/README_CN.md
- This repo is aimed to notify the community of development security by collecting reported smart contract issues
- This repo collects all info from public resources and part of analysis is generated by script along with manual checking
- This repo might not be perfectly accurate, please contact us or submit a pull request when you find something wrong
- This repo contains no unreported issue
- This repo might have duplicate names with popular projects, please do not over-decipher this
- This repo includes some Token contracts without vulnerabilities, while they fail to satisfy specifications
- This repo has a few problematic Token contracts that have already been fixed properly
- Visit
bad_tokens.all.csvfor a summary of all Token contracts affected - Visit
bad_tokens.top.csvfor a summary of top ranking Token contracts affected - Visit
ERC20_token_issue_list.mdfor a detailed description of all bugs and Token contracts affected - Visit 'How to contribute' if you find a mistake or anything missed in this repo
- 2018-08-13, AGC, a25-constructor-naming-error
- 2018-07-31, AMORCOIN, a24-getToken-anyone
- 2018-07-25, OPL, a23-fake-burn
- 2018-07-14, MDOT, a22-constructor-mistyping
- 2018-07-08, AMMBR, a1-batchtransfer-overflow
- 2018-06-25, TFD, a16-custom-call-abuse
- Add info of totalSupply, decimals, exchanges into Token lists
- 2018-06-20, ATN, a15-custom-fallback-bypass-ds-auth
- 2018-06-22, MORPH, a14-constructor-case-insensitive
- 2018-06-16, ICX, a11-pausetransfer-anyone
- 2018-06-12, PKT, a8-excess-mint-token-by-overflow
- 2018-06-08, ITC, b1-transfer-no-return
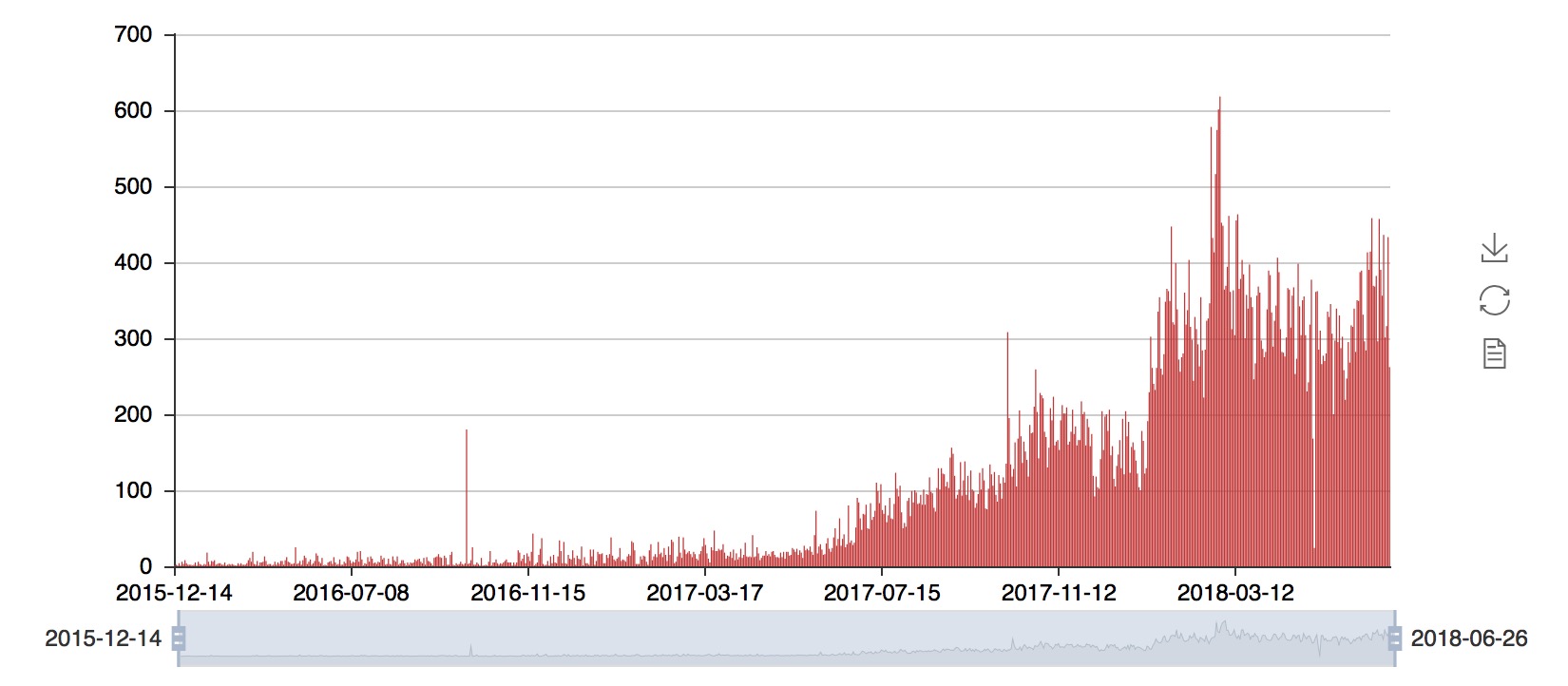
ERC20 standard is one of the most popular Ethereum token standards [1]. As of June 26th, 2018, more than 95,000 ERC20 token smart contracts have been deployed according to statistics from Etherscan. Here is a daily trend chart of ERC20 contracts created according to our statistics:
ERC20 Token specification has gone through challenges and improvements during its growth. Lots of critical security issues have been revealed, some of which have led to severe financial losses [2-11] for developers, investors, even Ethereum community as well.
On June 18th, 2016, the DAO hack caused a total loss of over 3,600,000 ethers(ETH) worth over a billion dollars, and the Ethereum hard-fork afterwards led to the Ethereum community breaking apart [2].
On April 22th, 2018, the attack on BeautyChain(BEC) contract hardly decreased the token price to zero via pouring astronomical tokens to exchanges through an integer overflow [3]. There are 10 other contracts at least containing this problem.
On April 25th, 2018, a similar integer overflow got uncovered in SMT. Hackers minted and dumped a tremendous amount of tokens, resulting in SMT's collapse [4]. There is one other contract at least containing this problem.
On May 20th, 2018, a critical logical flaw was found in EDU along with other three Token contracts (CVE-2018–11397, CVE-2018–11398), causing that users' balances could be transferred out randomly [5]. After further analysis, we caught this bug in at least 81 contracts [6].
On June 12, 2018, a series of overflow bug in ERC20 smart contracts got uncovered (CVE-2018-11687, CVE-2018-11809, CVE-2018-11810, CVE-2018-11811, CVE-2018-11812) [7]. We have revealed more than 800 contracts with the same problem after scanning over 20,000 contracts deployed on Etherscan [8].
Lots of ERC20 token contracts do not follow the ERC20 standard strictly, which is troublesome to developers of DApps on ERC20 tokens [12-14].
Thousands of deployed Token contracts referred to incorrect example code on Ethereum official website and OpenZeppelin, resulting in several functions failing to meet ERC20 standard. After upgrading Solidity compiler to 0.4.22, incompatibilities would arise and these contracts could not perform normal transactions on decentralized exchanges (DEX) or DApp in most cases [12], whereas a majority of DApp developing teams were off guard and unaware of such a problem.
Several Token contracts added redundant checks in standard approve(), requiring that the approved _amount smaller or equal to the current balance. However, it makes DEX employing protocols like 0x hard to finish approve() in advance, asking the Token developing team transfer a huge amount of tokens to the exchange's intermediate account ahead which violates the target of employing ERC20 standard and brings about inconvenience.
Since it is defined optional to set common querying interfaces like name(), symbol() and decimals() in ERC20 specification [1], many Token contracts left them out or named them differently, such as NAME(), SYMBOL() and DECIMALS(), making it harder for DEX and DApp developing.
Another point worth mentioning is that two events - Transfer and Approval should get fired under certain circumstances described by ERC20 specification [1]. In fact, many Token contracts left out Approval event referring to Ethereum official website [14]. This omission causes great difficulty for developers listening to relevant events, undermining the development of DApp ecosystem.
Statistical summaries from security organizations and experts indicate that critical vulnerabilities are hiding in smart contracts, taking the 'TOP 10 in 2018' by NCC group [15] as an example:
- Reentrancy
- Access Control
- Integer Overflow
- Unchecked Return Values For Low Level Calls
- Denial of Service
- Bad Randomness
- Front-Running
- Time manipulation
- Short Address Attack
- Unknown Unknowns
This might be just the tip of an iceberg. Recent research together with the aforementioned point of view state clearly that the scale of problems in smart contracts deployed on Ethereum may go beyond our imagination.
We made a collection of past bugs and vulnerabilities, including:
- vulnerabilities in Token contracts
- incompatibilities due to inconsistency with ERC20
- excessive authorities of Token administrators [16]
There are many projects in Ethereum community contributing to the ecosystem of smart contracts, such as 'A guide to smart contract security best practices' [17] maintained by Consensys and 'OpenZeppelin, a framework to build secure smart contracts on Ethereum' [18] developed by OpenZeppelin.
Also, we found the fact that a majority of issues in buggy Token contracts come from referring, copying and modifying others' code without caution. Also, using incorrect sample code is an origin of bugs. It is difficult for beginners and developers of smart contracts to determine whether a contract snippet from main net contains bugs and identify these issues in seconds.
We would maintain this collection to:
- provide a reference and learning materials of common bugs in ERC20 token contracts
- help ERC20 token contract developers to develop correct and secure contracts
- notice DApp developers of incompatible/buggy/vulnerable ERC20 token contracts
- warn exchanges and investors of potential risks in incompatible/buggy/insecure ERC20 tokens
- Descriptions of common vulnerabilities
- List of deployed buggy token contracts
- List of nonstandard token contracts
awesome-buggy-erc20-tokens
├── token_dict.json
├── token_detail_dict.json
├── ERC20_token_issue_list_CN.md
├── issues.json
├── bad_tokens.all.csv
├── bad_tokens.all.json
├── bad_tokens.top.csv
├── bad_tokens.top.json
├── raw/
├── csv/
├── json/
├── gen_token_detail_dict.py
└── gen_list_from_raw.pytoken_dict.jsonlists addresses and basic info of ERC20 contracts collected by CoinMarketCaptoken_detail_dict.jsonlists addresses and detailed info of ERC20 contracts collected by CoinMarketCapERC20_token_issue_list.mdlists detailed descriptions of known bugs.issues.jsonmaps between known bugs and indexes.bad_tokens.all.csvalong withbad_tokens.all.jsonare lists of all buggy Token contracts in CSV and JSON formats.bad_tokens.top.csvalong withbad_tokens.top.jsonare lists of top ranking buggy Token contracts in CSV and JSON formats.raw/,csv/andjson/list all known bugs and addresses of affected contracts in formats of plain text, CSV and JSON.gen_token_detail_dict.pyis a script to updatetoken_detail_dict.jsongen_list_from_raw.pyis a script to generate.csvand.jsonlists above.
As shown below, lists in CSV and JSON help developers to browse and search for addresses of given contracts with reported vulnerabilities.
addr,category,name,symbol,exchanges,totalSupply,decimals,info
0x014B50466590340D41307Cc54DCee990c8D58aa8,[B6],ICOS,ICOS,@HitBTC@Tidex,560417,6,_
0x093e5C256Ff8B32c7F1377f4C20e331674C77F00,[A2],Dignity,DIG,@Livecoin,3000000000,8,_
{
"0x014B50466590340D41307Cc54DCee990c8D58aa8": {
"decimals": 6,
"exchanges": [
"HitBTC",
"Tidex"
],
"info": "_",
"issues": {
"no-symbol": true
},
"name": "ICOS",
"rank": 316,
"symbol": "ICOS",
"totalSupply": 560417
},
"0x093e5C256Ff8B32c7F1377f4C20e331674C77F00": {
"decimals": 8,
"exchanges": [
"Livecoin"
],
"info": "_",
"issues": {
"totalsupply-overflow": true
},
"name": "Dignity",
"rank": 613,
"symbol": "DIG",
"totalSupply": 3000000000
}
}We hope this collection can contribute to the Ethereum ecosystem by maintaining and updating in a long period and definitely welcome contributions to this collection.
For now we only maintain detailed information of token contracts (totalSupply, decimals, exchanges) that have market caps on CoinMarketCap. If you find any other incompatible/buggy/vulnerable ERC20 token contracts, please update token_dict.json and run script gen_token_detail_dict.py.
If you find other bugs not listed in this collection, please update in the following process.
- Add the name and description of the bug with reference to
ERC20_token_issue_list.md - Create a new file with the bug name in
rawdirectory and fill in the address of affected contracts - Add the name and index of the new bug to
issues.json - Run
python3 gen_list_from_raw.py -i raw/* -o bad_tokensin the repo root - Check the update and send us a pull request
If you have any questions or ideas, please join our discussion on Gitter.
- Add more 'Excessive Authorities' issues:
- Minting tokens
- Setting trading price
- Manipulate other accounts
- Loopring https://loopring.io/
- DEx.top https://dex.top/
- ConsenSys China https://consensys.net/
- Chaitin Tech https://www.chaitin.cn/
- [1] ERC-20 Token Standard, Nov 19, 2015
- [2] Understanding The DAO Hack for Journalists, Jun 19, 2016
- [3] A disastrous vulnerability found in smart contracts of BeautyChain (BEC), Apr 23, 2018
- [4] SmartMesh Announcement on Ethereum Smart Contract Overflow Vulnerability
- [5] SECBIT: 智能合约红色预警:四个Token惊爆逻辑漏洞,归零风险或源于代码复制, May 24, 2018
- [6] SECBIT: 围观!81个智能合约惊现同一漏洞,是巧合?还是另有玄机?, Jun 3, 2018
- [7] Tsinghua-360 Research Center of Enterprise Security: ERC20智能合约整数溢出系列漏洞披露, Jun 12, 2018
- [8] ChainDD: 【得得预警】ERC20智能合约又现大量整数溢出漏洞, Jun 12, 2018
- [9] Alert! Another integer overflow vulnerability just found in HXG smart contract, May 19, 2018
- [10] UselessEthereumToken(UET), ERC20 token, allows attackers to steal all victim’s balances (CVE-2018–10468), May 3, 2018
- [11] Bugged Smart Contract FuturXE: How Could Someone Mess up with Boolean? (CVE-2018–12025), Jun 6, 2018
- [12] An Incompatibility in Ethereum Smart Contract Threatening dApp Ecosystem, Jun 8, 2018
- [13] Redundant Check in ERC20 Smart Contracts’ approve(), Jun 15, 2018
- [14] token-erc20: add event Approval to follow eip20
- [15] DASP - Top 10 of 2018
- [16] PeckShield: Highly-Manipulatable ERC20 Tokens Identified in Multiple Top Exchanges, Jun 9, 2018
- [17] A guide to smart contract security best practices
- [18] OpenZeppelin, a framework to build secure smart contracts on Ethereum
- [19] 360 0KEE Team: 以太坊智能合约Hexagon存在溢出漏洞, May 18, 2018
- [20] SlowMist:ATN 披露特殊场景下的以太坊合约重大漏洞, Jun 20, 2018
- [21] BCSEC: 一些智能合约存在笔误,一个字母可造成代币千万市值蒸发!, Jun 22, 2018
- [22] LianAn:小心!智能合约再爆高危漏洞,两大加密货币直接变废纸!, Jun 6, 2018
- [23] PeckShield: New allowAnyone Bug Identified in Multiple ERC20 Smart Contracts, May 23, 2018