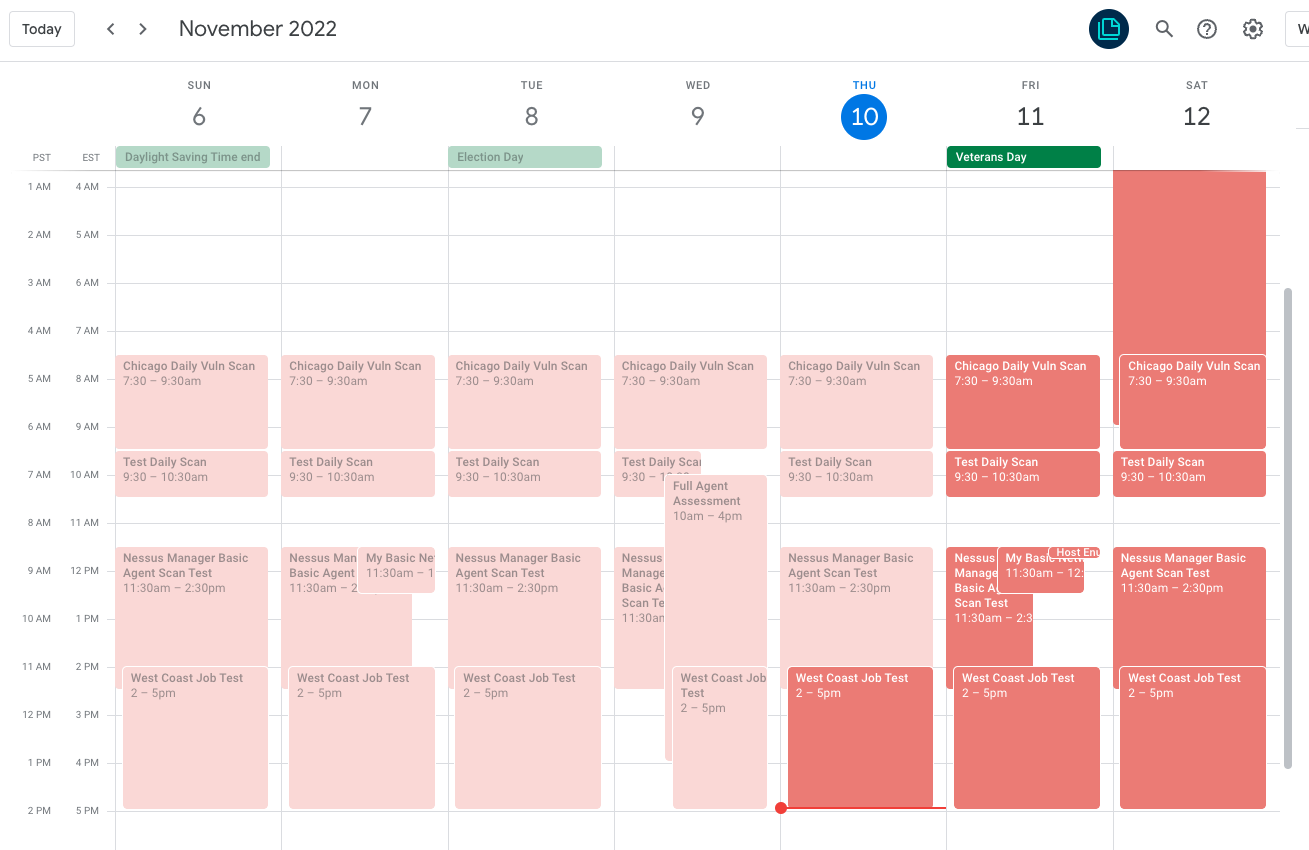
Creates an .ics file that can be imported into your calendar management tool of choice to show when Tenable Nessus Network scans or agent assessments run and how long they're expected to take. Supports Tenable.sc, Tenable.io VM, and Nessus (all flavors).
This tool is not an officially supported Tenable project
Use of this tool is subject to the terms and conditions identified below, and is not subject to any license agreement you may have with Tenable
Docker is recommended; be sure to pass the proper .env file. Works well on Docker for Mac or Windows.
docker run -d --rm --env-file .env -v ${PWD}/:/home/scan_calendar/output/ -v ${PWD}/logs:/home/scan_calendar/output/logs tecnobabble/tenb_scan_calendar:latest
You can also just run from Python directly (recommended for Docker on Linux):
(Requires python 3.6 or higher; suggest pyenv)
pip install -r requirements.txt
python scan_calendar.py
The output will be a file called tenable_scans.ics produced. Load this file into Google/Outlook Calendar.
You could also run this container/script on a schedule and copy the file to a webserver; subscribe to the produced calendar file Google/Outlook and it will auto update when changes are made to the relevant scan jobs.
- Must be T.sc 5.19 or above
- Must enable API auth application wide
- Must create or use existing API keys for a user that can "Create Scans" as part of their role (Vulnerability Analyst, Security Analyst, Security Manager or custom) and that can manage all objects for all groups.
- Works for direct agent scans and network based scans
- Must be run once per tenable.sc 'organization' (and rename the ics file after each run)
- Get API keys for a user that can manage/see all scans
- Get API keys for a user that can manage/see all scans
Tested on python 3.10+; will likely work on 3.6+
Sample .env file in same folder as script:
SC_ACCESS_KEY=aaaaaaabbbbbbccccddddeeeffff1234
SC_SECRET_KEY=aaaaaaabbbbbbccccddddeeeffff1234
SC_ADDRESS=10.0.0.100
SC_PORT=443
IO_URL=https://cloud.tenable.com
IO_ACCESS_KEY=aaaaaaabbbbbbccccddddeeeffff1234
IO_SECRET_KEY=aaaaaaabbbbbbccccddddeeeffff1234
NESSUS_URL=https://10.0.0.101:8834
NESSUS_ACCESS_KEY=aaaaaaabbbbbbccccddddeeeffff1234
NESSUS_SECRET_KEY=aaaaaaabbbbbbccccddddeeeffff1234
- If a max_scan time or enough scans have previously run (3), the script will define/estimate future scan lengths. If not available, defaults to 1 hour.
- To subscribe to a calendar, the .ics file has to be public if using a cloud email service like Google/Outlook.com. It has to be reachable from your internal calendar software install otherwise (ex: Outlook installed locally on your computer).
Add "DEBUG=TRUE" to your env file and re-run the script. See the logs in the generated 'logs' folder. If you're still unsure, open an Issue.
Support Direct Agent ScansPull network scan completetion times to estimate future runtimemaintain state to support deleted events- Support multiple orgs
Support t.ioSupport Nessus (all flavors)- Support T.sc Director
support running from dockersupport debug mode
Made possible largely by ics-py (https://github.com/ics-py/ics-py)
Pull requests are welcome. For major changes, please open an issue first to discuss what you would like to change.