This AWS Security Survival Kit will allow you to set up minimal alerting on typical suspicious activities on your AWS Account.
You all know that CloudTrail is now the bare minimum service to activate on a newly created AWS Account to track all activities on your AWS account. It is nice, but suspicious activities will not come from themself to you. You still have to check periodically if something goes wrong in multiple services and console.
With these CloudFormation templates, you will bring security observability to your AWS account, it's complementary to the GuardDuty service (There are no built-in alerts on GuardDuty).
Using this kit, you will deploy CloudWatch EventRules and CW alarms on all suspect activities below:
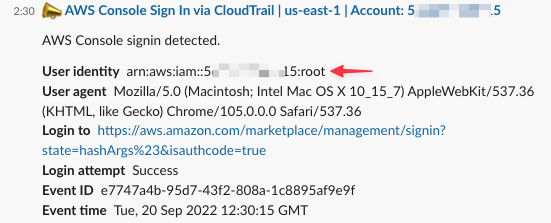
- Root User activities
- CloudTrail changes (
StopLogging,DeleteTrail,UpdateTrail) - AWS Personal Health Dashboard Events
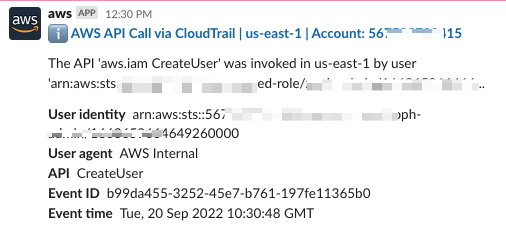
- IAM Users Changes (
Create,Delete,Update,CreateAccessKey, etc..) - MFA Monitoring (
CreateVirtualMFADeviceDeactivateMFADeviceDeleteVirtualMFADevice, etc..) - Unauthorized Operations (
Access Denied,UnauthorizedOperation) - Failed AWS Console login authentication (
ConsoleLoginFailures) - EBS Snapshots Exfiltration (
ModifySnapshotAttribute,SharedSnapshotCopyInitiatedSharedSnapshotVolumeCreated) - AMI Exfiltration (
ModifyImageAttribute) - Who Am I Calls (
GetCallerIdentity)
AlarmRecipient: Recipient for the alerts (ie: hello@zoph.io)Project: Name of the Project (ie: aws-security-survival-kit)Description: Description of the Project (ie: Bare minimum ...)LocalAWSRegion: Region where your workloads and CloudTrail are located (ie:eu-west-1)CTLogGroupName: Cloudtrail CloudWatch LogGroup name
Setup the correct parameters in the Makefile, then run the following command:
$ make deploy
Setup AWS Chatbot for best experience to get notified directly on Slack.
- 🏴☠️ AWS Security Boutique: zoph.io
- 💌 AWS Security Digest Newsletter
- 🐦 Twitter: zoph