The final OAuth secured .NET API code sample, referenced in my blog at https://authguidance.com:
- The API takes finer control over OAuth domain specific claims and uses a certified JOSE library
- The API uses JSON request logging and Elasticsearch log aggregation, for measurability
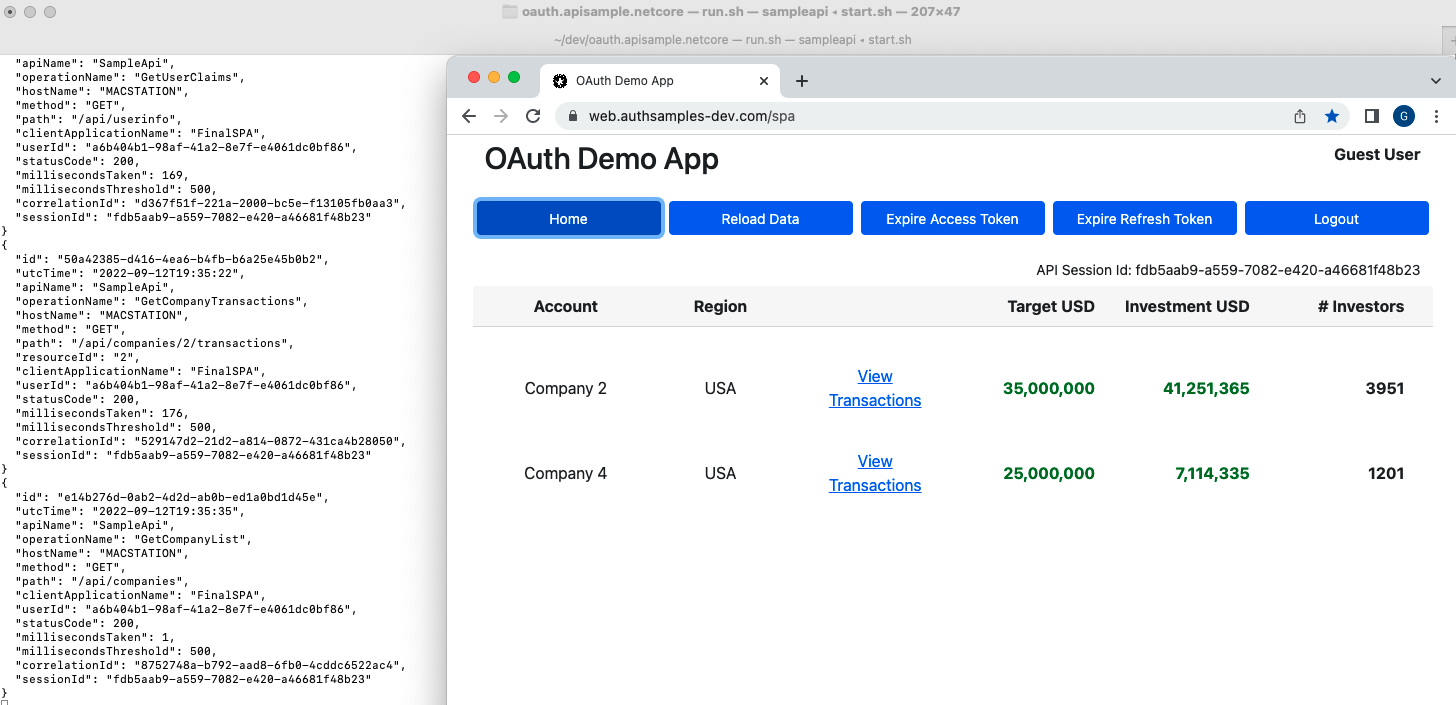
The API can run as part of an OAuth end-to-end setup, to serve my blog's UI code samples.
Running the API in this manner forces it to be consumer focused to its clients:
The API's clients are UIs, which get user level access tokens by running an OpenID Connect code flow.
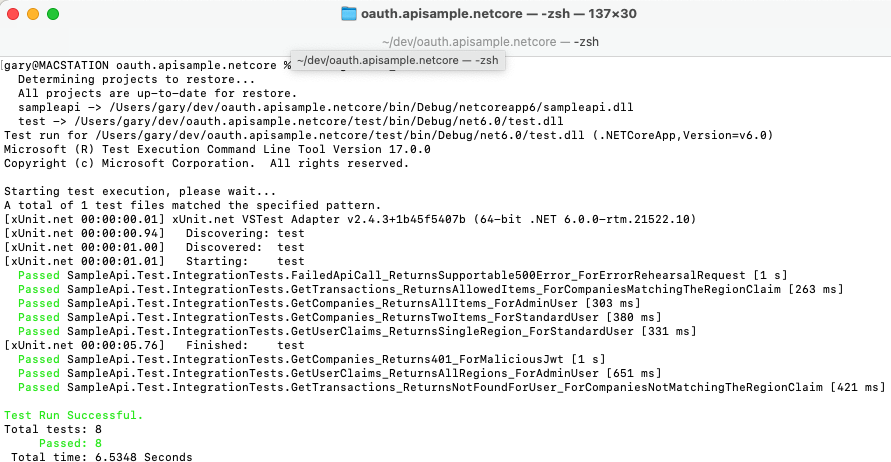
For productive test driven development, the API instead mocks the Authorization Server:
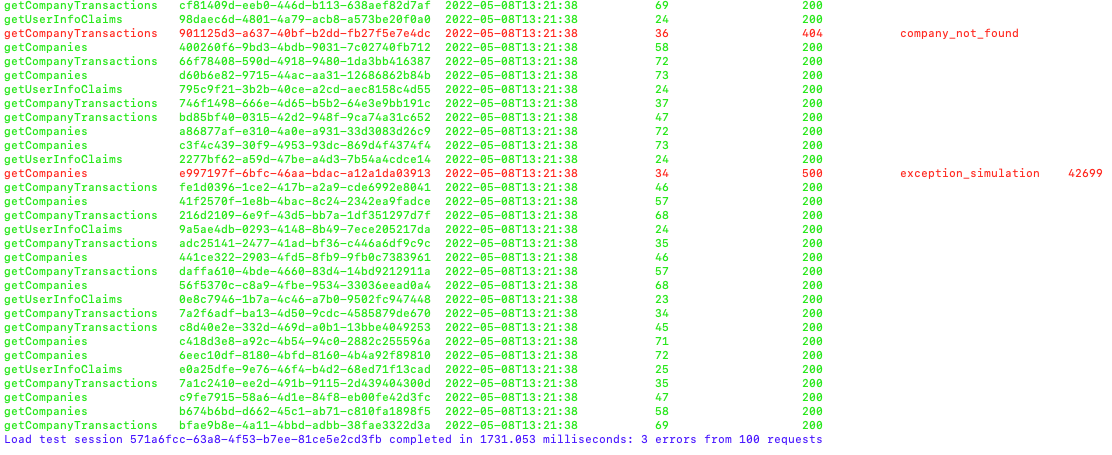
A basic load test uses Tasks to fire 5 parallel requests at a time at the API.
This ensures no concurrency problems, and error rehearsal is used to verify that the API is supportable:
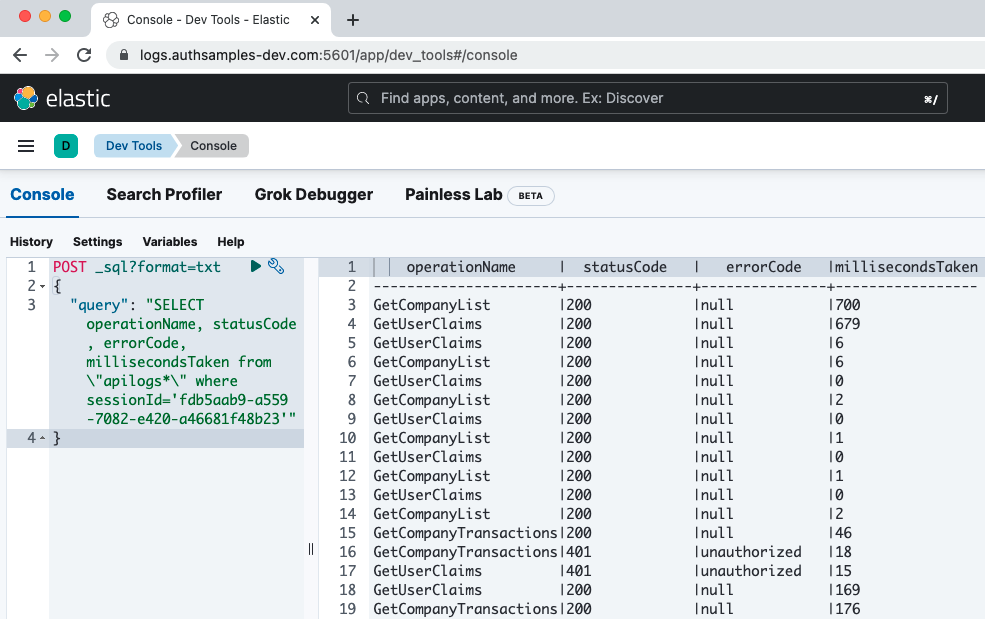
API logs can be analysed in use case based manner by running Elasticsearch SQL and Lucene queries.
Follow the Technical Support Queries for some people friendly examples:
Ensure that .NET 7+ is installed, then run the API with this command:
./start.shConfigure DNS by adding these domains to your hosts file:
127.0.0.1 localhost api.authsamples-dev.com login.authsamples-dev.com
Then call an endpoint over port 446:
curl -k https://api.authsamples-dev.com:446/api/companiesConfigure .NET SSL trust for the root CA at ./certs/authsamples-dev.ca.pem.
Stop the API, then re-run it with a test configuration:
./testsetup.shThen run integration tests and a load test:
./integration_tests.sh
./load_test.sh- See the Overview Page for instructions on how to run the API
- See the OAuth Integration Page for the security implementation
- See the Non Functional Behaviour page for a summary of overall qualities
- C# and .NET 7 are used to implement the REST API
- The Kestrel web server is used to host the API over SSL
- AWS Cognito is used as the default Authorization Server
- The jose-jwt Library is used to manage in memory validation of JWTs
- The API is designed for cloud native deployment to Kubernetes