GitHub Action to upload and scan files with VirusTotal.
If you are interested, check out my other ![]() GitHub Actions!
GitHub Actions!
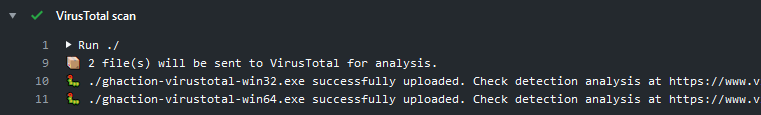
This action can be used to scan local files with VirusTotal:
name: build
on:
pull_request:
push:
jobs:
build:
runs-on: ubuntu-latest
steps:
-
name: Checkout
uses: actions/checkout@v2
-
name: Set up Go
uses: actions/setup-go@v2
-
name: Build
run: |
GOOS=windows GOARCH=386 go build -o ./ghaction-virustotal-win32.exe -v -ldflags "-s -w"
GOOS=windows GOARCH=amd64 go build -o ./ghaction-virustotal-win64.exe -v -ldflags "-s -w"
-
name: VirusTotal Scan
uses: crazy-max/ghaction-virustotal@v2
with:
vt_api_key: ${{ secrets.VT_API_KEY }}
files: |
./ghaction-virustotal-win32.exe
./ghaction-virustotal-win64.exeYou can also use this action to scan assets of a published release on GitHub when a release event is triggered:
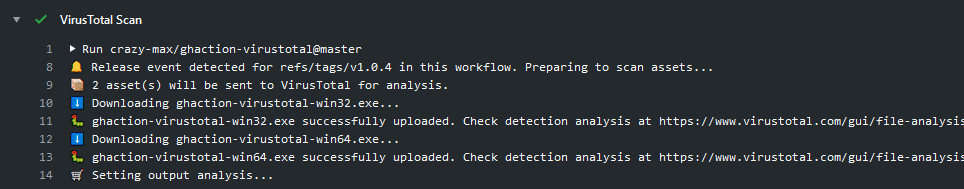
name: released
on:
release:
types: [published]
jobs:
virustotal:
runs-on: ubuntu-latest
steps:
-
name: VirusTotal Scan
uses: crazy-max/ghaction-virustotal@v2
with:
vt_api_key: ${{ secrets.VT_API_KEY }}
github_token: ${{ github.token }}
files: |
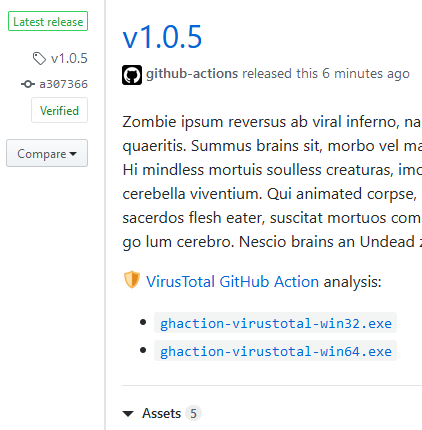
*.exeIf you set update_release_body: true input, analysis link(s) will be appended to the release body and will look like this:
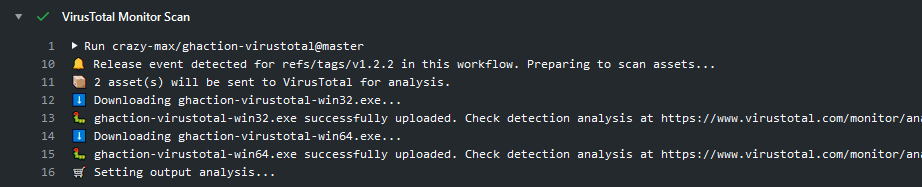
To scan your assets through VirusTotal Monitor you can use the following workflow:
name: build
on:
pull_request:
push:
jobs:
build:
runs-on: ubuntu-latest
steps:
-
name: Checkout
uses: actions/checkout@v2
-
name: Set up Go
uses: actions/setup-go@v2
-
name: Build
run: |
GOOS=windows GOARCH=386 go build -o ./ghaction-virustotal-win32.exe -v -ldflags "-s -w"
GOOS=windows GOARCH=amd64 go build -o ./ghaction-virustotal-win64.exe -v -ldflags "-s -w"
-
name: VirusTotal Monitor Scan
uses: crazy-max/ghaction-virustotal@v2
with:
vt_api_key: ${{ secrets.VT_API_KEY }}
vt_monitor: true
monitor_path: /ghaction-virustotal
files: |
./ghaction-virustotal-*.exeFollowing inputs can be used as step.with keys
| Name | Type | Description |
|---|---|---|
vt_api_key |
String | VirusTotal API key to upload assets (required) |
files |
String | Newline-delimited list of path globs/patterns for asset files to upload for analysis (required) |
vt_monitor |
Bool | If enabled, files will be uploaded to VirusTotal Monitor endpoint (default false) |
monitor_path¹ |
String | A path relative to current monitor user root folder to upload files (default /) |
update_release_body² |
Bool | If enabled, analysis link(s) will be appended to the release body (default false) |
github_token³ |
String | GitHub Token used to create an authenticated client for GitHub API as provided by secrets (default ${{ github.token }}) |
- ¹ Only available if
vt_monitoris enabled.- ² Only available if release event is triggered in your workflow.
- ³ Required if release event is triggered in your workflow.
Following outputs are available
| Name | Type | Description |
|---|---|---|
analysis |
String | Analysis results formatted as <filename>=<analysisURL> (comma separated) |
Since Dependabot
has native GitHub Actions support,
to enable it on your GitHub repo all you need to do is add the .github/dependabot.yml file:
version: 2
updates:
# Maintain dependencies for GitHub Actions
- package-ecosystem: "github-actions"
directory: "/"
schedule:
interval: "daily"All kinds of contributions are welcome 🙌! The most basic way to show your support is to star 🌟 the project, or to raise issues 💬 You can also support this project by becoming a sponsor on GitHub 👏 or by making a Paypal donation to ensure this journey continues indefinitely! 🚀
Thanks again for your support, it is much appreciated! 🙏
MIT. See LICENSE for more details.