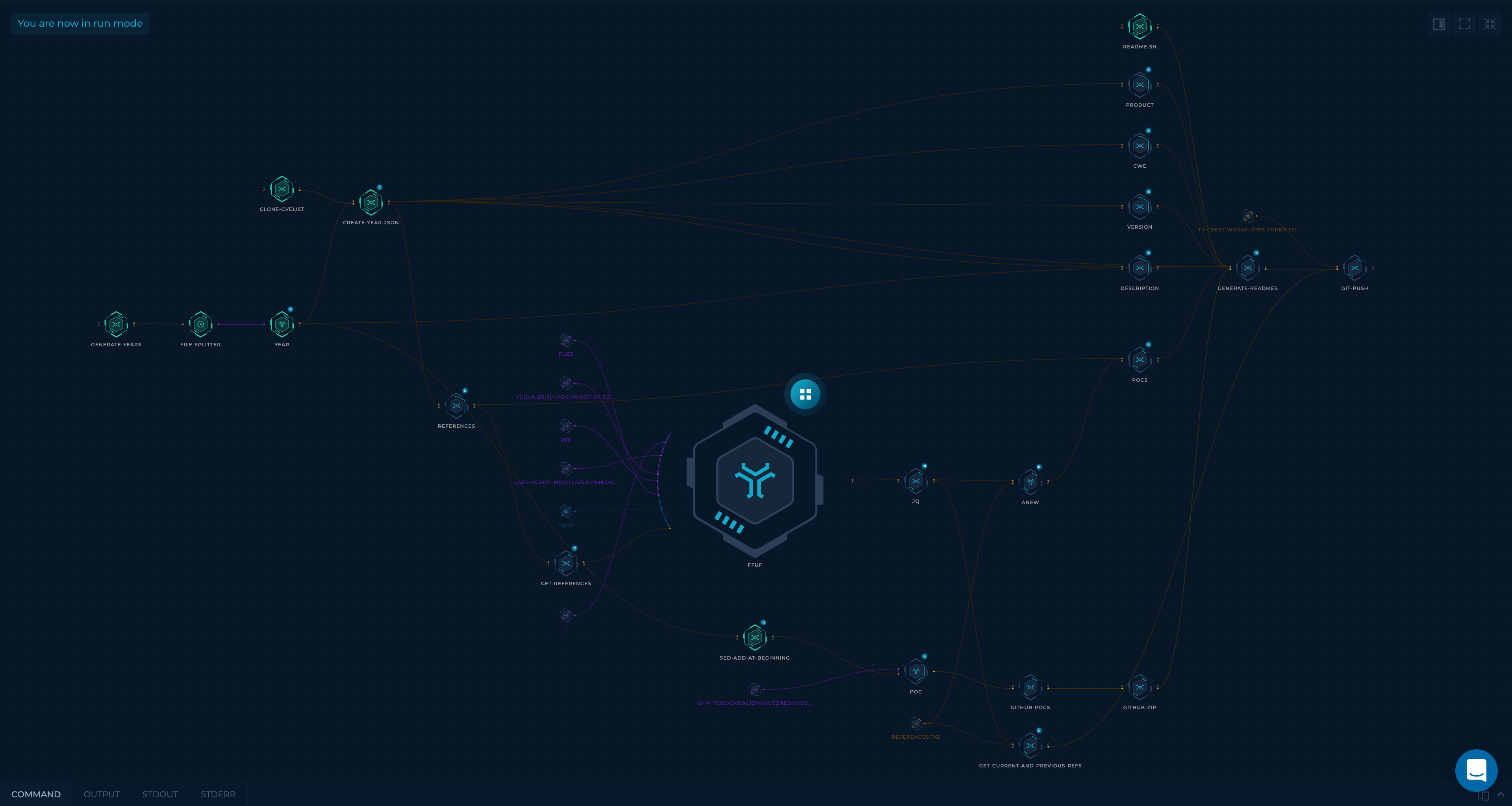
Trickest Workflow used:
- Collect CVE details from cvelist (Shout out to CVE Project!)
- Split CVEs up by year.
- Find PoCs for each CVE using 2 techniques:
-
References
- Gather each CVE's
References. - Check if any of them points to a PoC using
ffufand a list of keywords
Regex:
(?i)[^a-z0-9]+(poc|proof of concept|proof[-_]of[-_]concept)[^a-z0-9]+(Thanks @joohoi!)
Note: ffuf is awesome for more purposes than just content discovery.
- Gather each CVE's
-
Github
Search GitHub for repositories with find-gh-poc (release soon!) that mention the CVE ID.
-
- Merge all of the found PoCs.
- Generate GitHub badges for each affected software version using shields.io.
- Write everything into easy-to-read markdown files.
As described, almost everything in this repository is generated automatically. We carefully designed the workflow (and continue to develop it) to ensure the results are as accurate as possible.
- Browse around, find a nice PoC, and test away!
Watchthe repository to receive notifications about new PoCs as soon as they go public.- Search for a specific product(s) (and possibly version) to find all public exploits related to it.
- Monitor the atom feed for a specific product(s).
All contribtutions/ideas/suggestions are welcome! Create a new ticket via GitHub issues or tweet at us @trick3st.
We believe in the value of tinkering; cookie-cutter solutions rarely cut it. Sign up for a demo on trickest.com to customize this workflow to your use case, get access to many more workflows, or build your own from scratch!